We create a lot of content for various clients. On this page, we’ve collected examples of content created in the past that show different content types, styles, and formats.
You are welcome to copy for your own personal use. For commercial use — if you wish to use it in your own work context — please email us about credit/attribution.
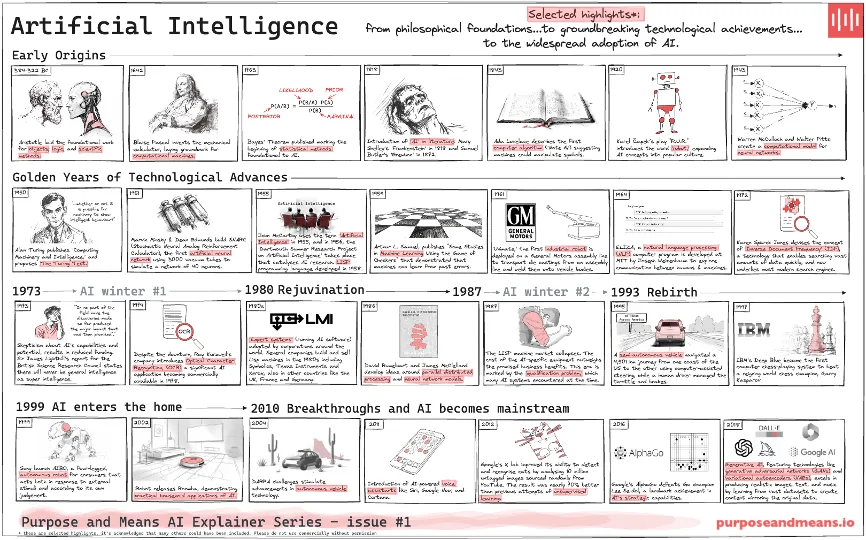
Early Origins of AI
A timeline of key milestones in the history of AI, from philosophical foundations to the recent rise of mainstream adoption.
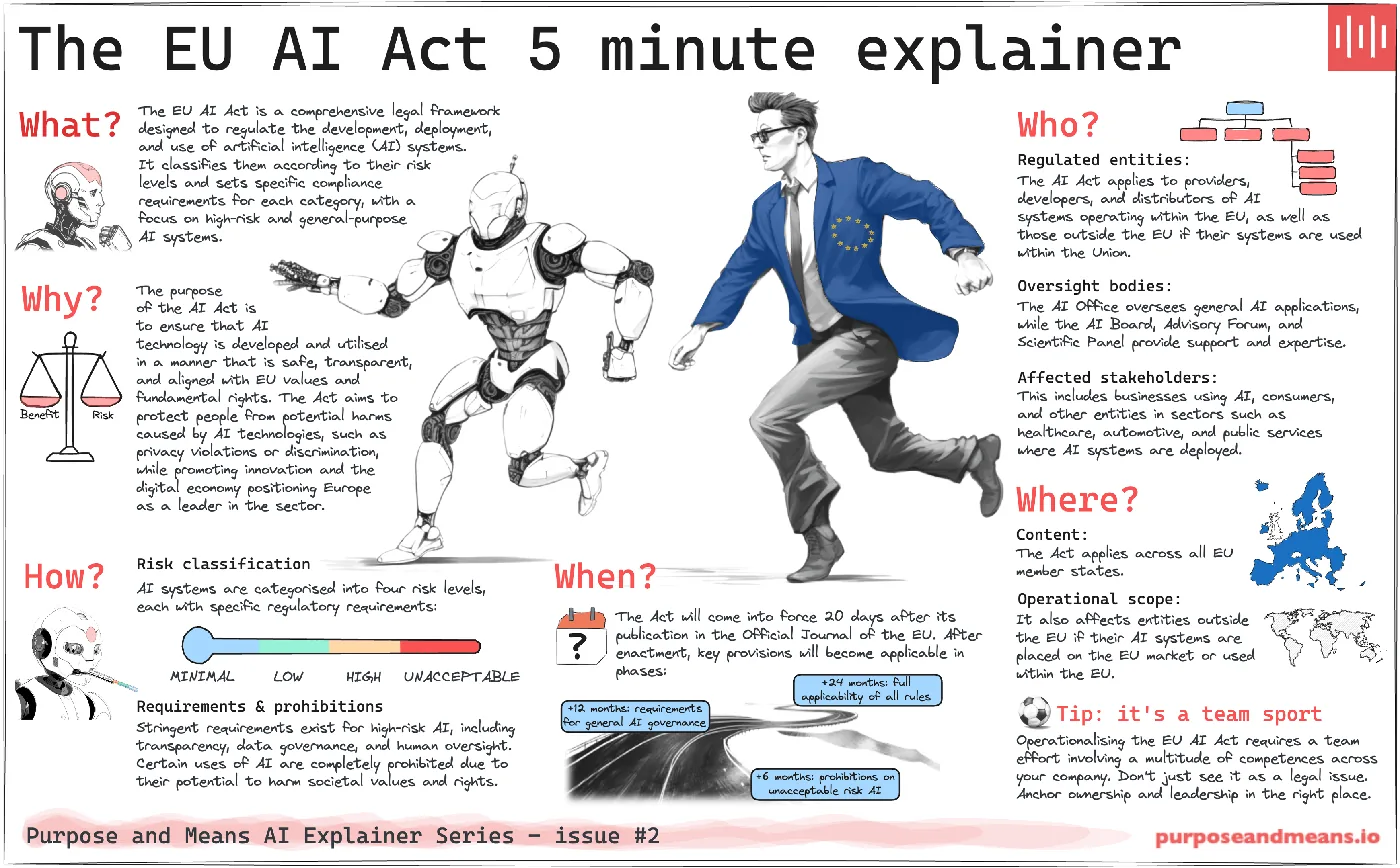
EU AI Act 5 Minute Explainer
A visual summary of the EU AI Act, outlining its risk-based approach, key compliance requirements, and categories of regulated AI systems.
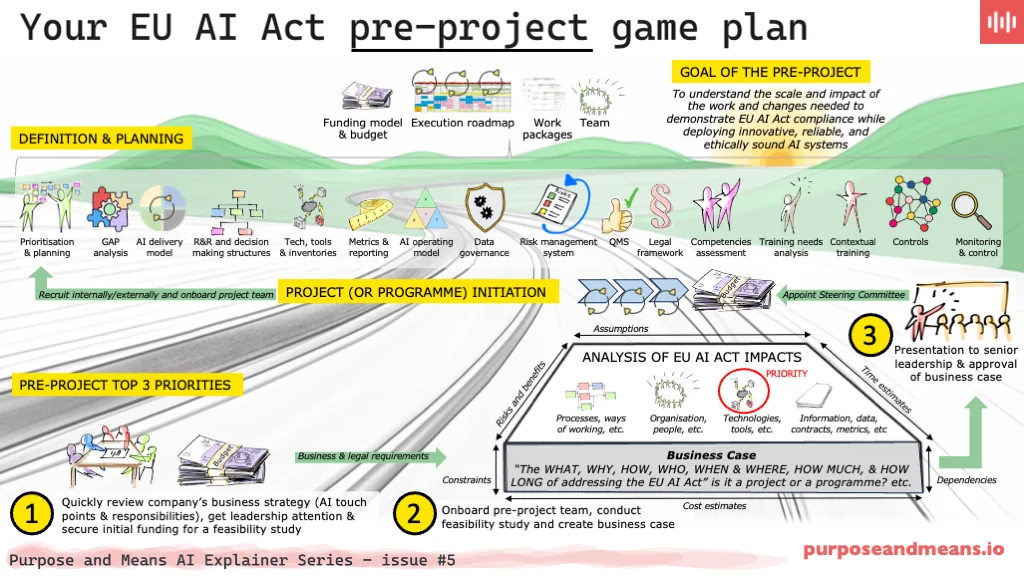
EU AI Act Pre-Project Game Plan
A pre-project game plan for EU AI Act compliance, emphasising strategic planning, team onboarding, and impact analysis.
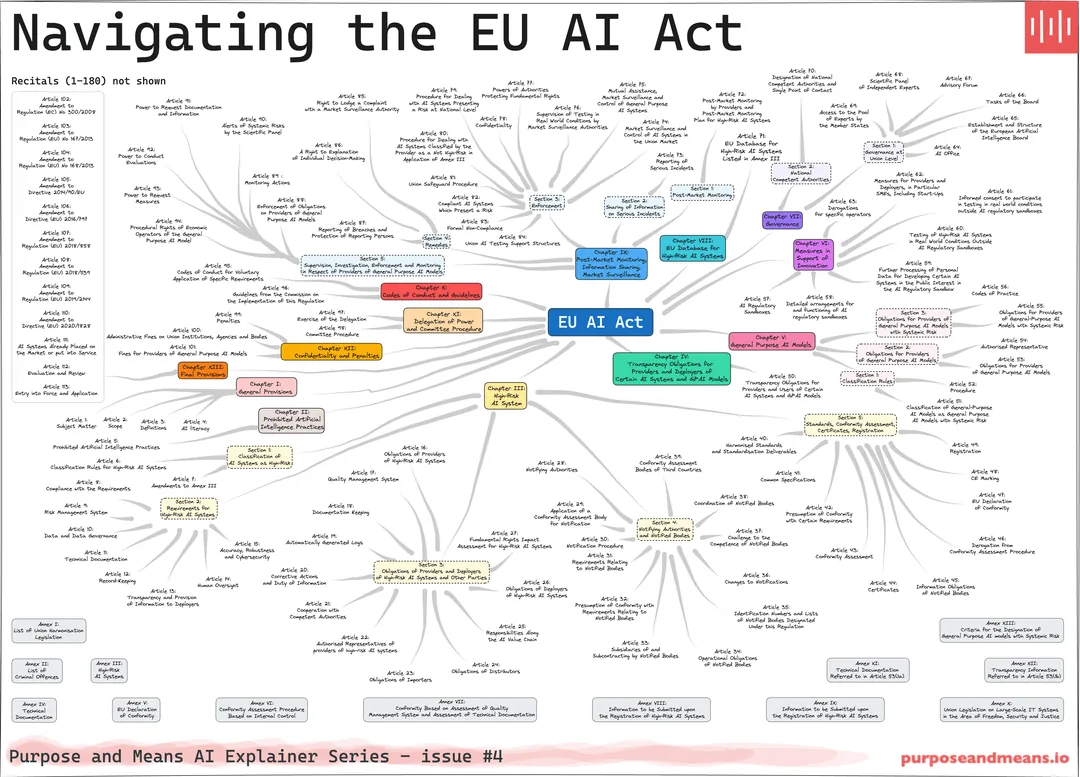
EU AI Act Mind Map
A visual mapping of the structure and chapters of the EU AI Act, detailing its main regulatory sections, referenced articles, and annexes.
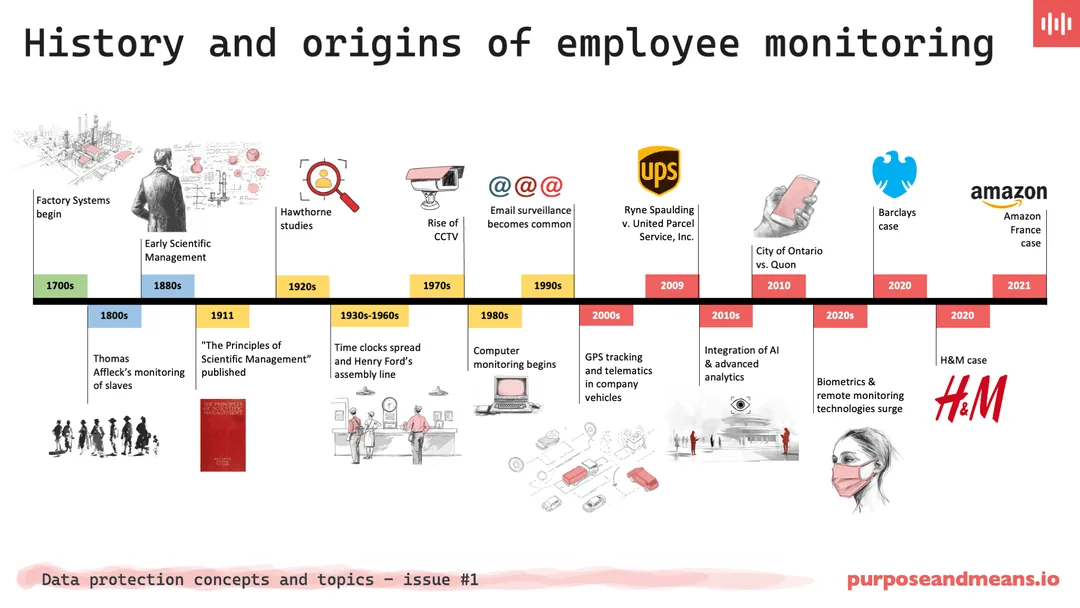
History and Origins of Employee Monitoring
An historical timeline of employee monitoring, tracing its evolution from factory systems through CCTV, GPS tracking, AI analytics, and biometric monitoring.
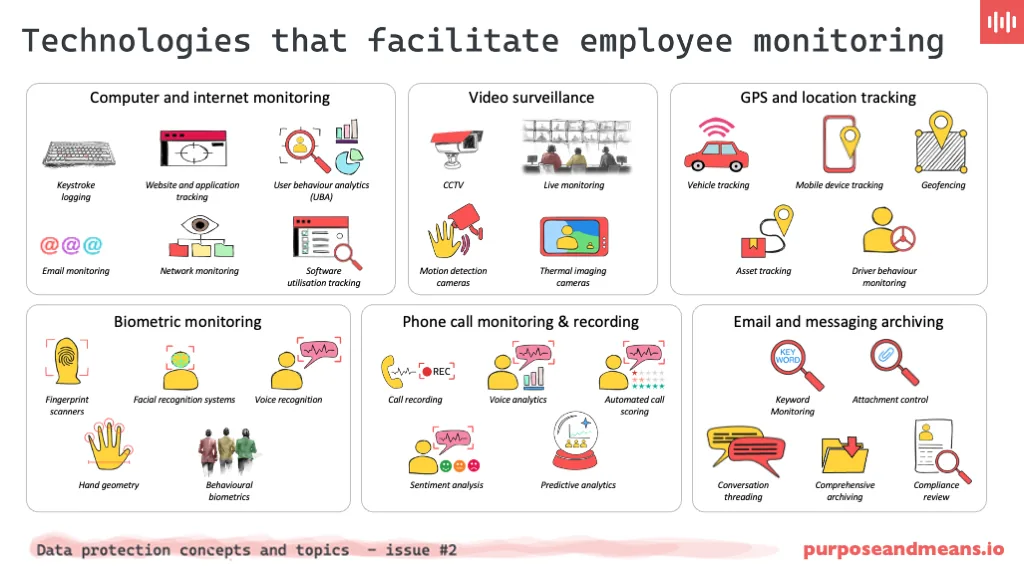
Technologies that Facilitate Employee Monitoring
A summary of the main technologies used in employee monitoring, including computer monitoring, video surveillance, GPS tracking, and biometrics.
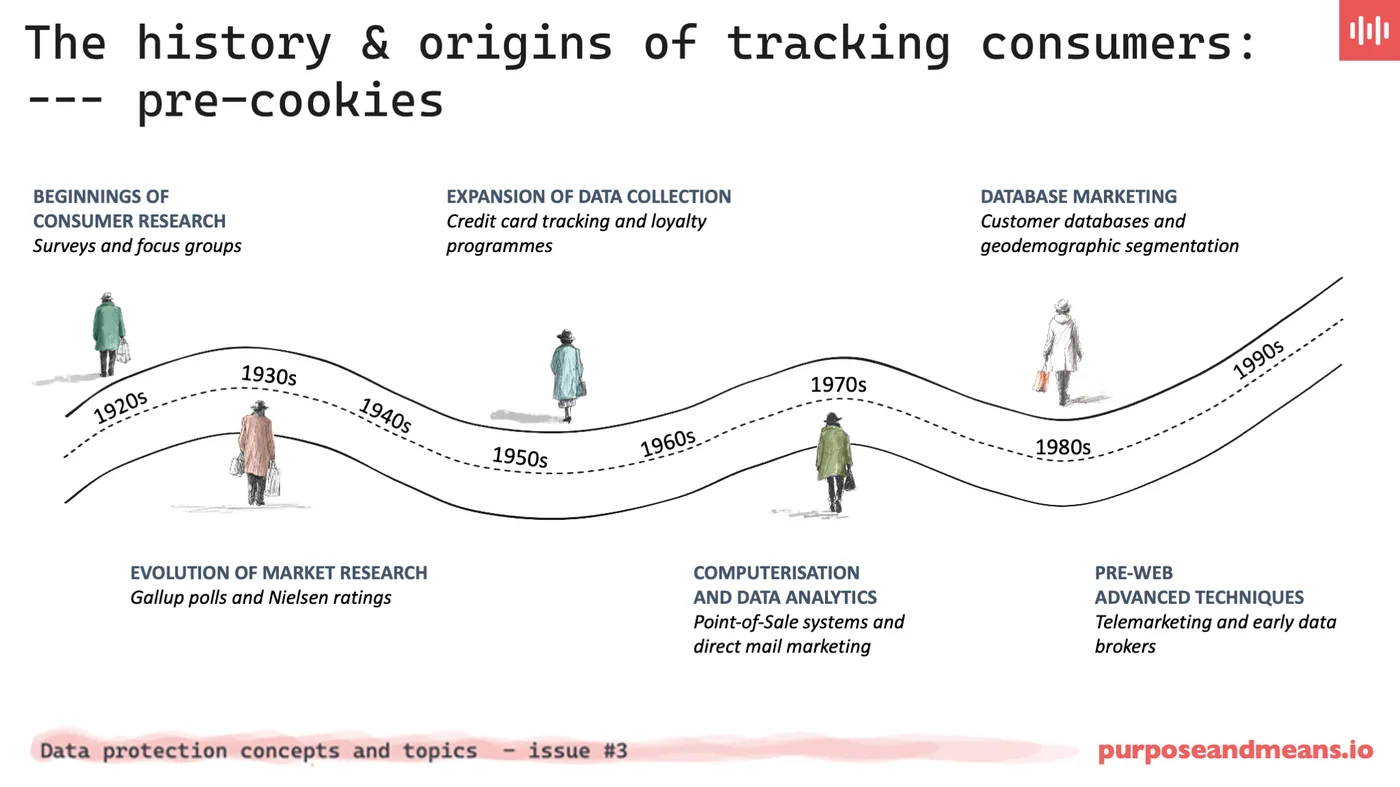
History of Tracking Consumers — Pre Cookies
An overview of consumer tracking before cookies, covering survey research, credit card tracking, database marketing, and pre-web analytics.
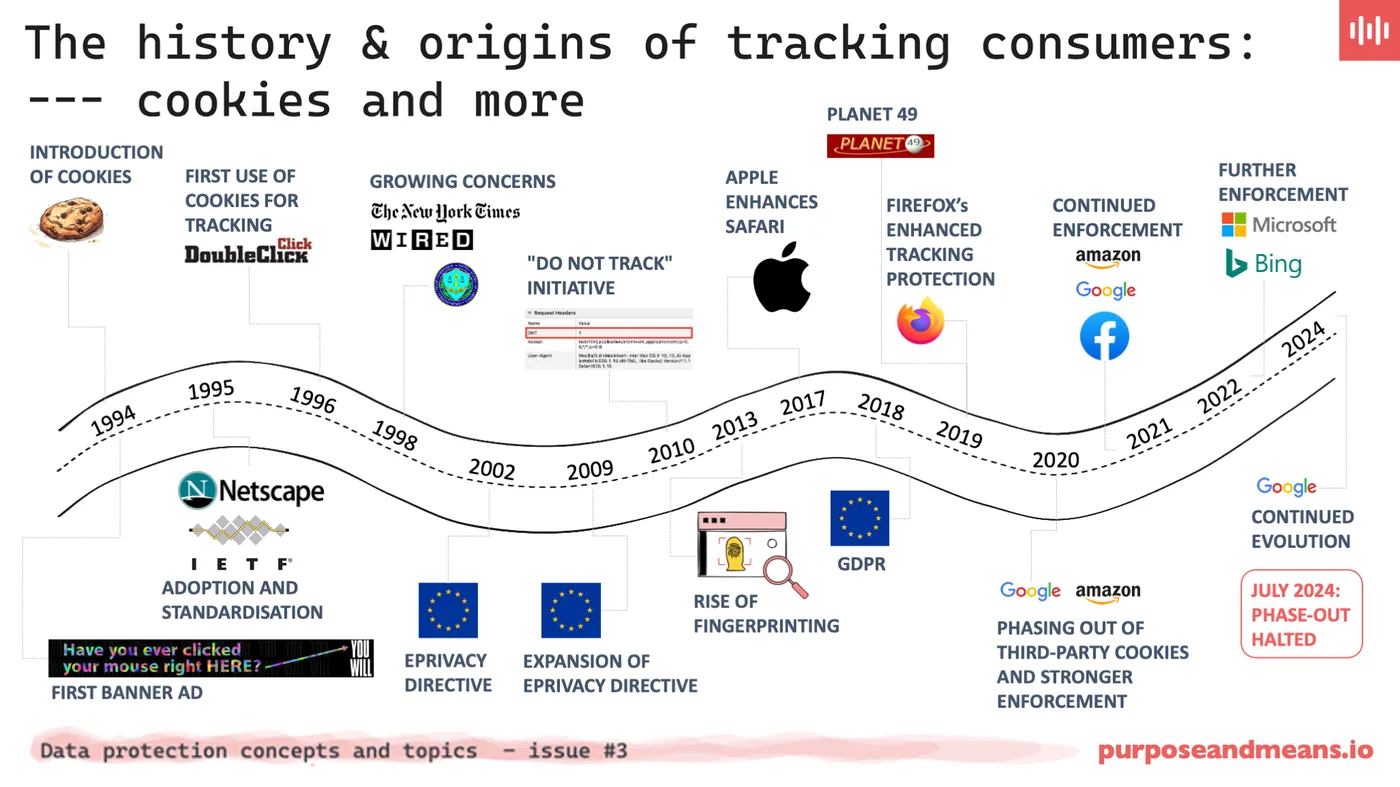
History and Origins of Tracking Consumers
Illustrates the evolution of consumer tracking with cookies, from adoption through rising privacy concerns, regulatory actions, and third-party cookie restrictions.
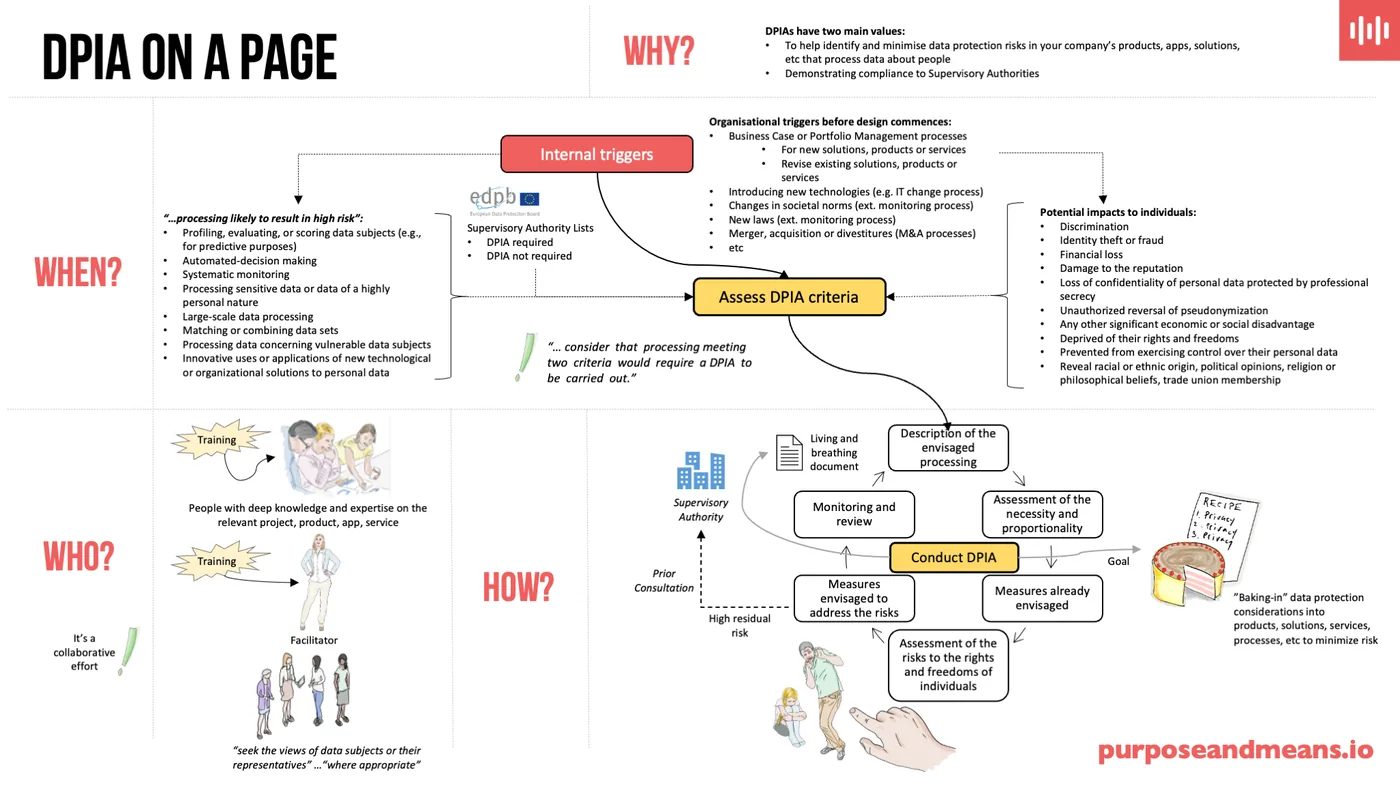
DPIA on a Page
A high-level overview of DPIA essentials, explaining purpose, key triggers, assessment criteria, team roles, and integration into business processes.
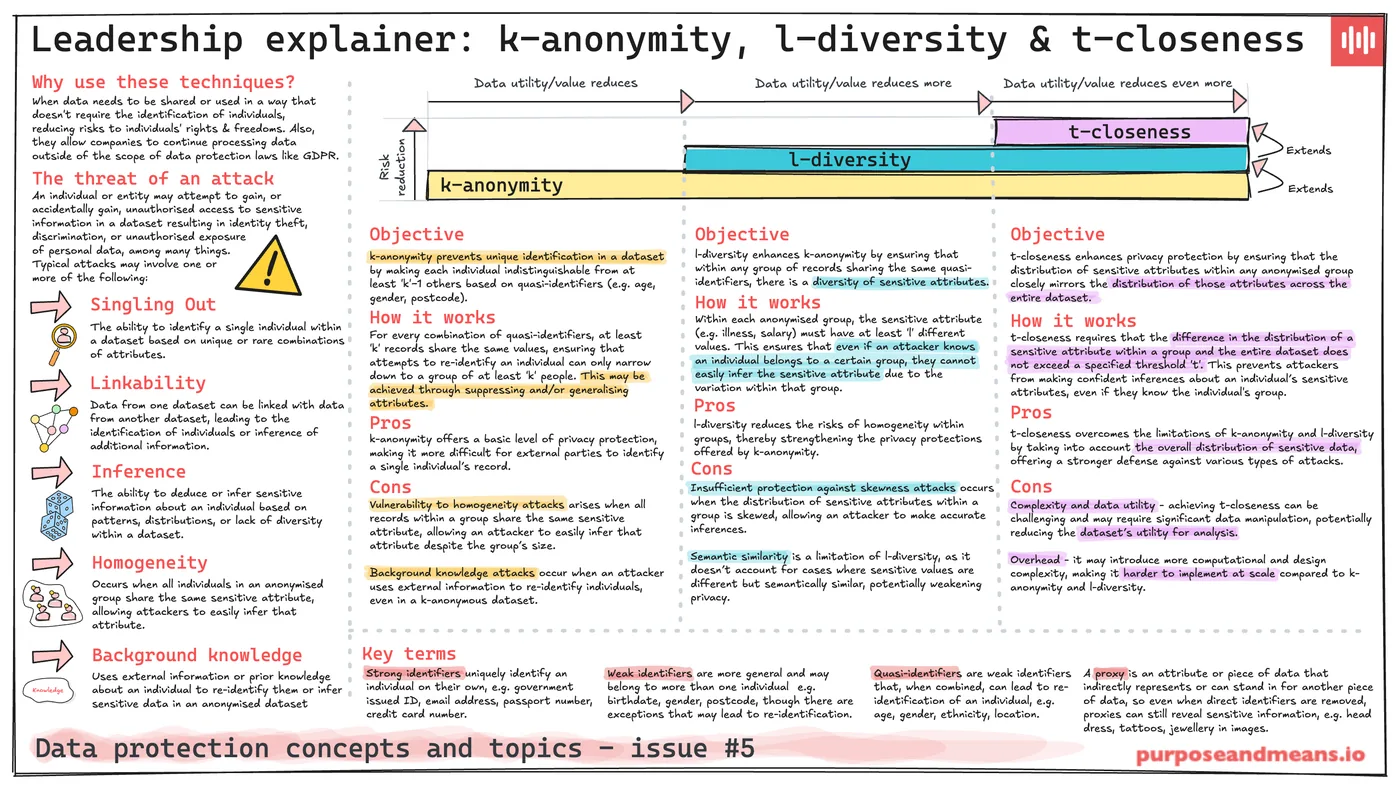
k-anonymity, l-diversity & t-closeness
Explains the principles, pros, and cons of these data anonymisation techniques and the types of attacks they mitigate or leave vulnerable.
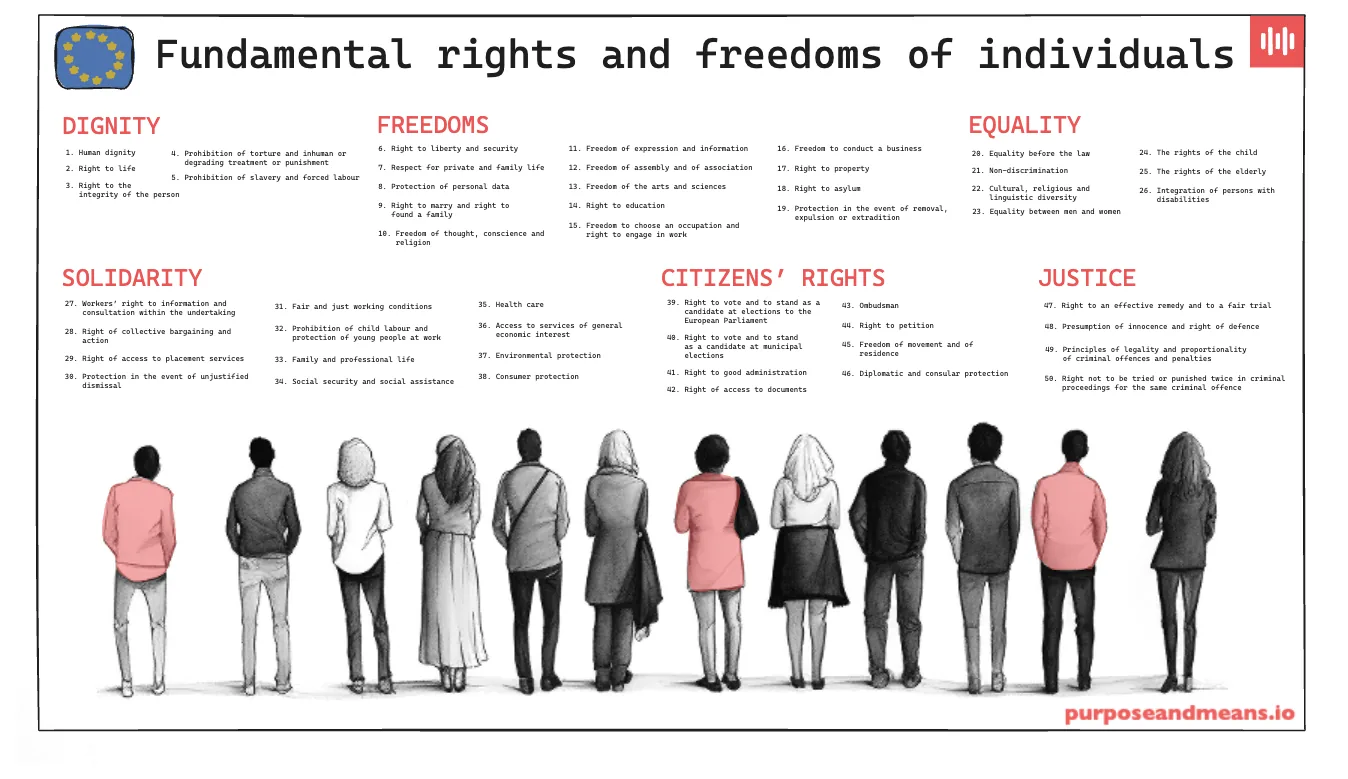
EU Fundamental Rights and Freedoms of Individuals
An overview of the main categories of fundamental rights and freedoms protected under the EU Charter, including dignity, equality, and justice.
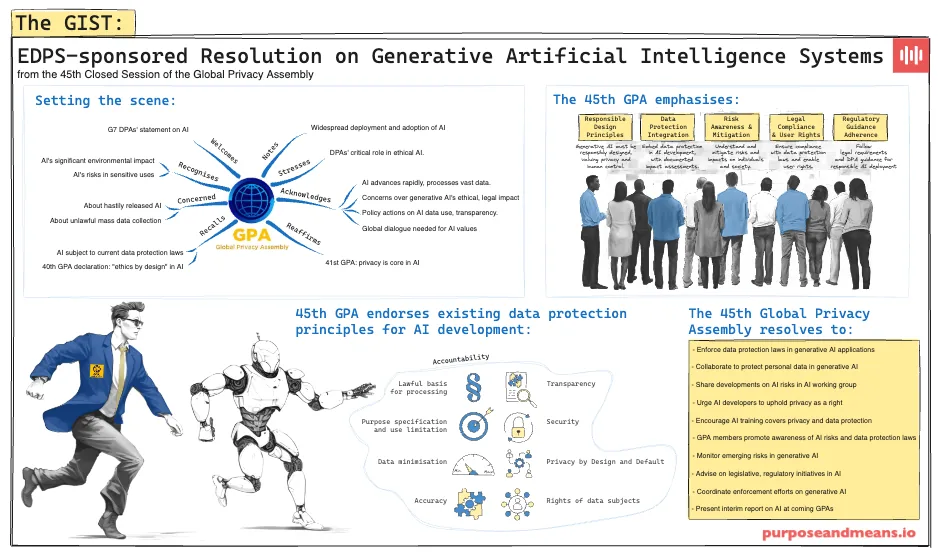
EDPS Sponsored Resolution on GenAI
Summarises the EDPS-sponsored resolution from the 45th Global Privacy Assembly on responsible design, data protection, and regulatory advancement for generative AI.
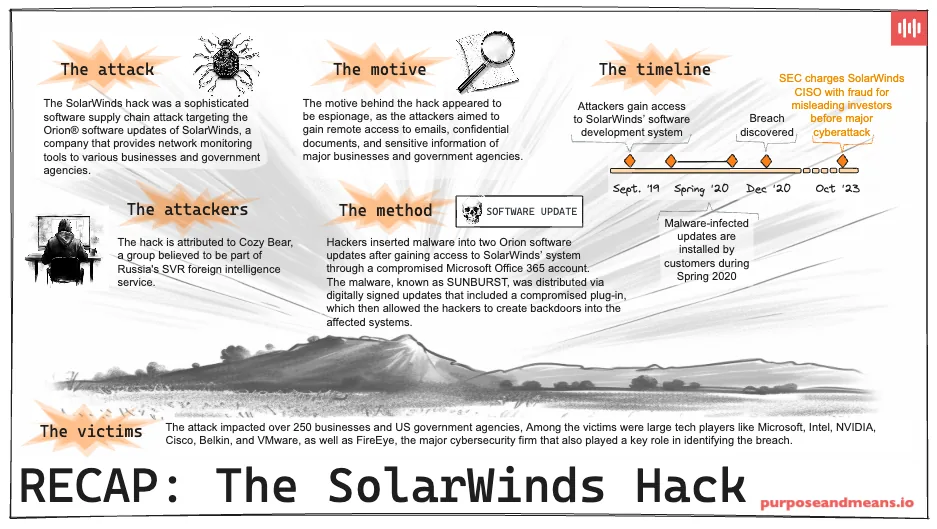
The SolarWinds Hack on a Page
Recaps the SolarWinds hack, describing the supply chain attack's method, attribution to Cozy Bear, and impact on over 250 organisations.
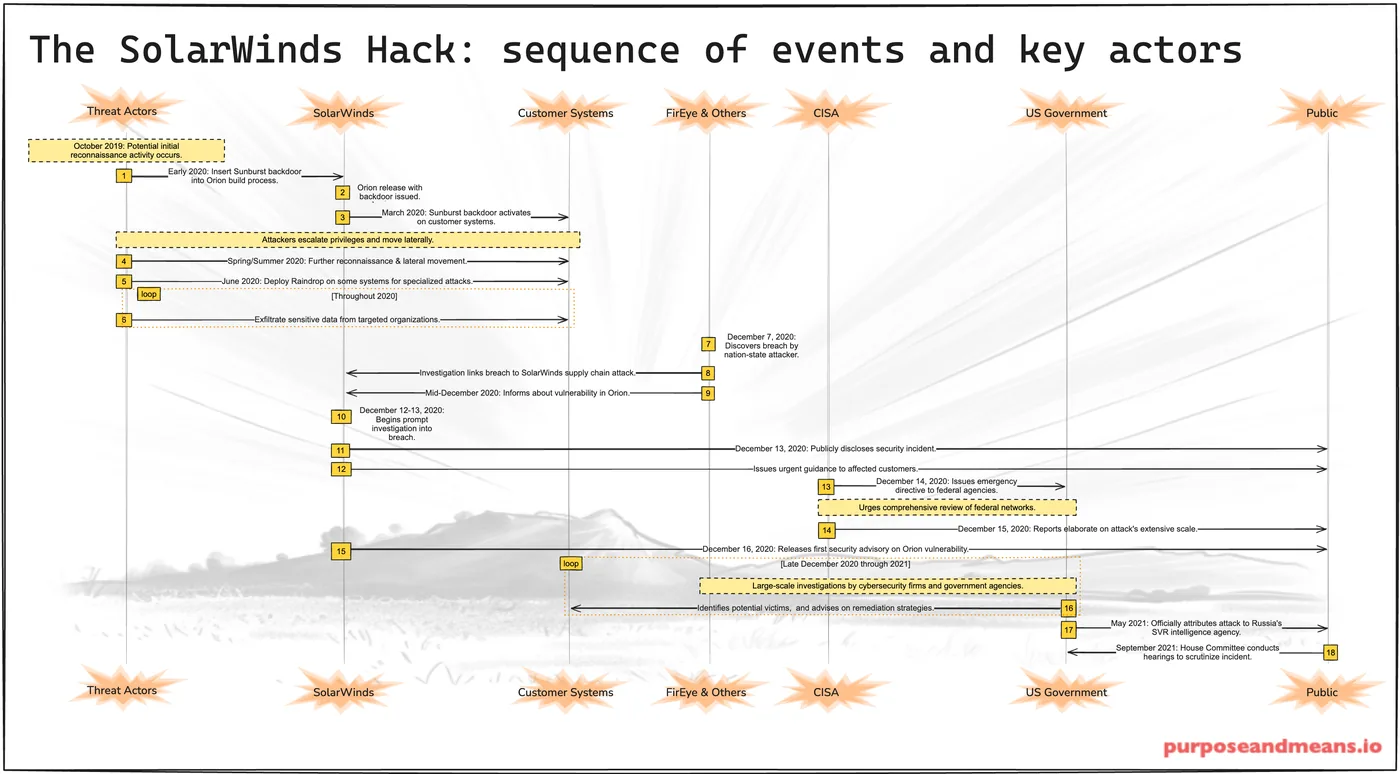
The SolarWinds Hack: Sequence of Events
Diagrams the sequence of events and key actors in the SolarWinds hack, from initial reconnaissance through public disclosure and attribution to Russia's SVR.
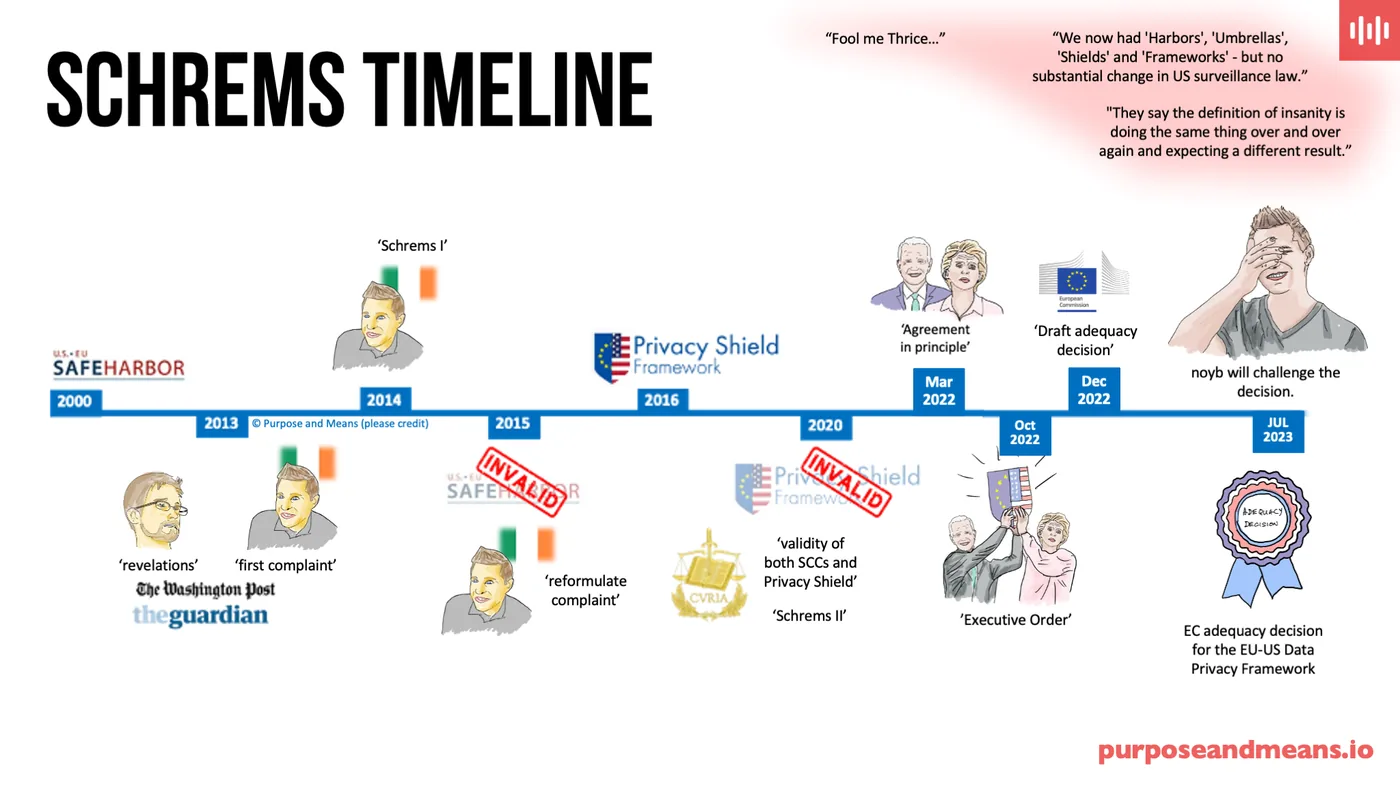
Schrems Timeline
Presents the timeline of the Schrems legal challenges against EU-US data transfer mechanisms, from Safe Harbor through to the EU-US Data Privacy Framework.
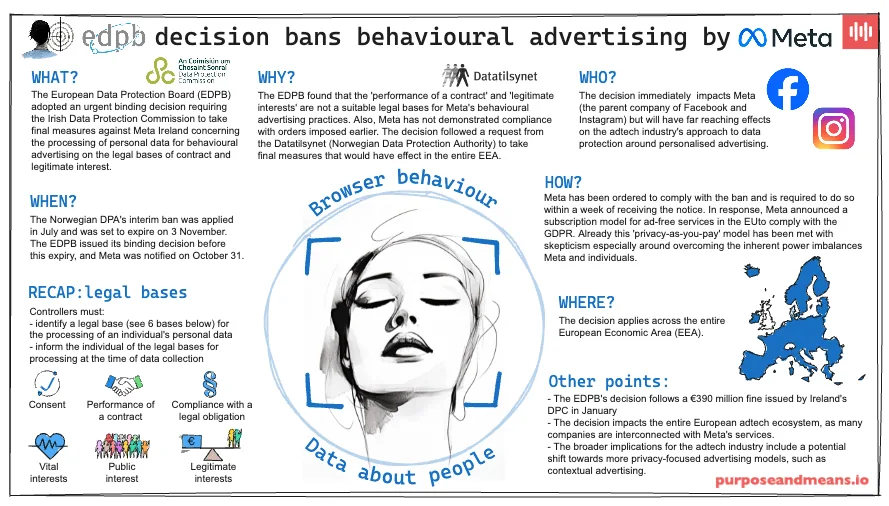
EDPB Decision Bans Behavioural Advertising
Explains the EDPB's urgent decision banning behavioural advertising by Meta in the EEA and its industry-wide implications for data protection.
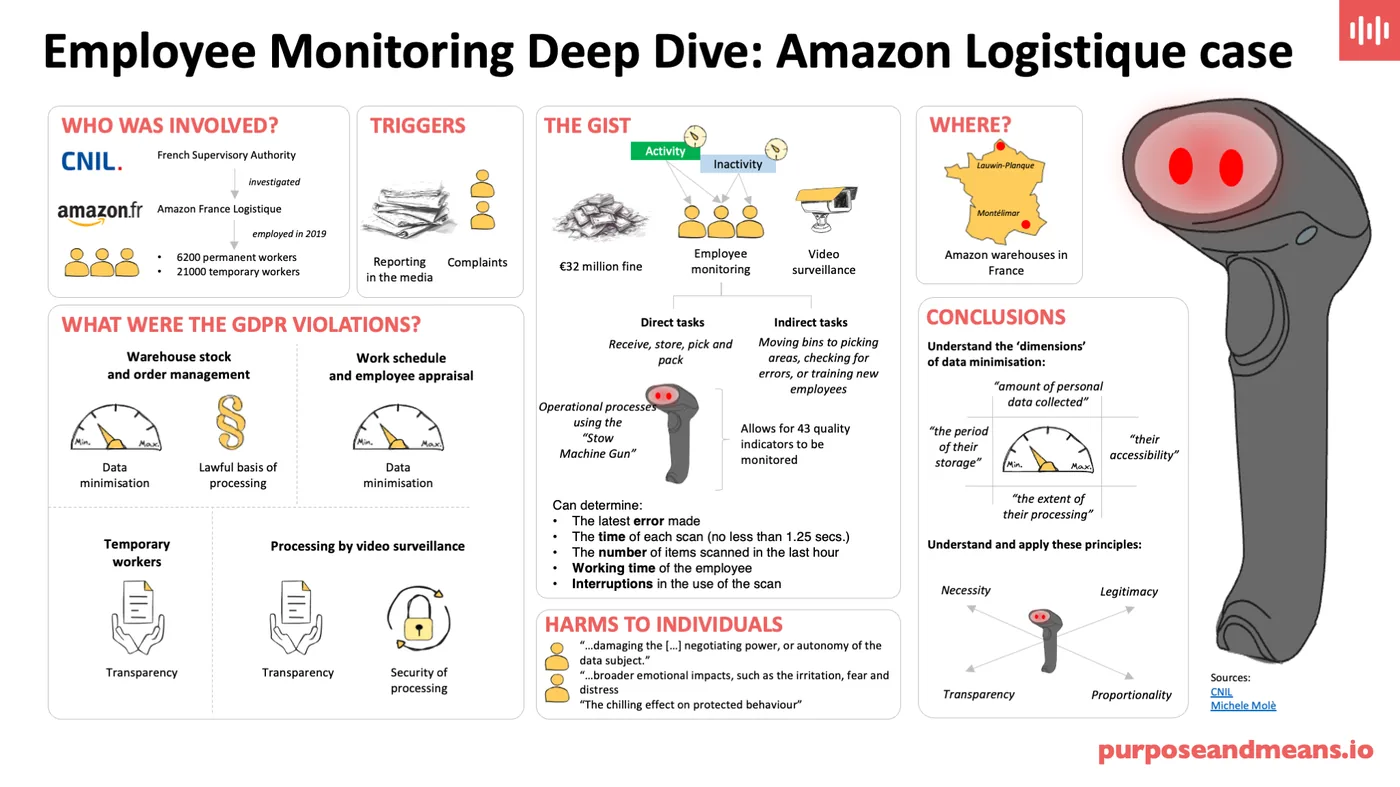
Amazon Logistique Case
Analyses the Amazon Logistique case, detailing a €32 million GDPR fine for unlawful and excessive employee monitoring practices in French warehouses.
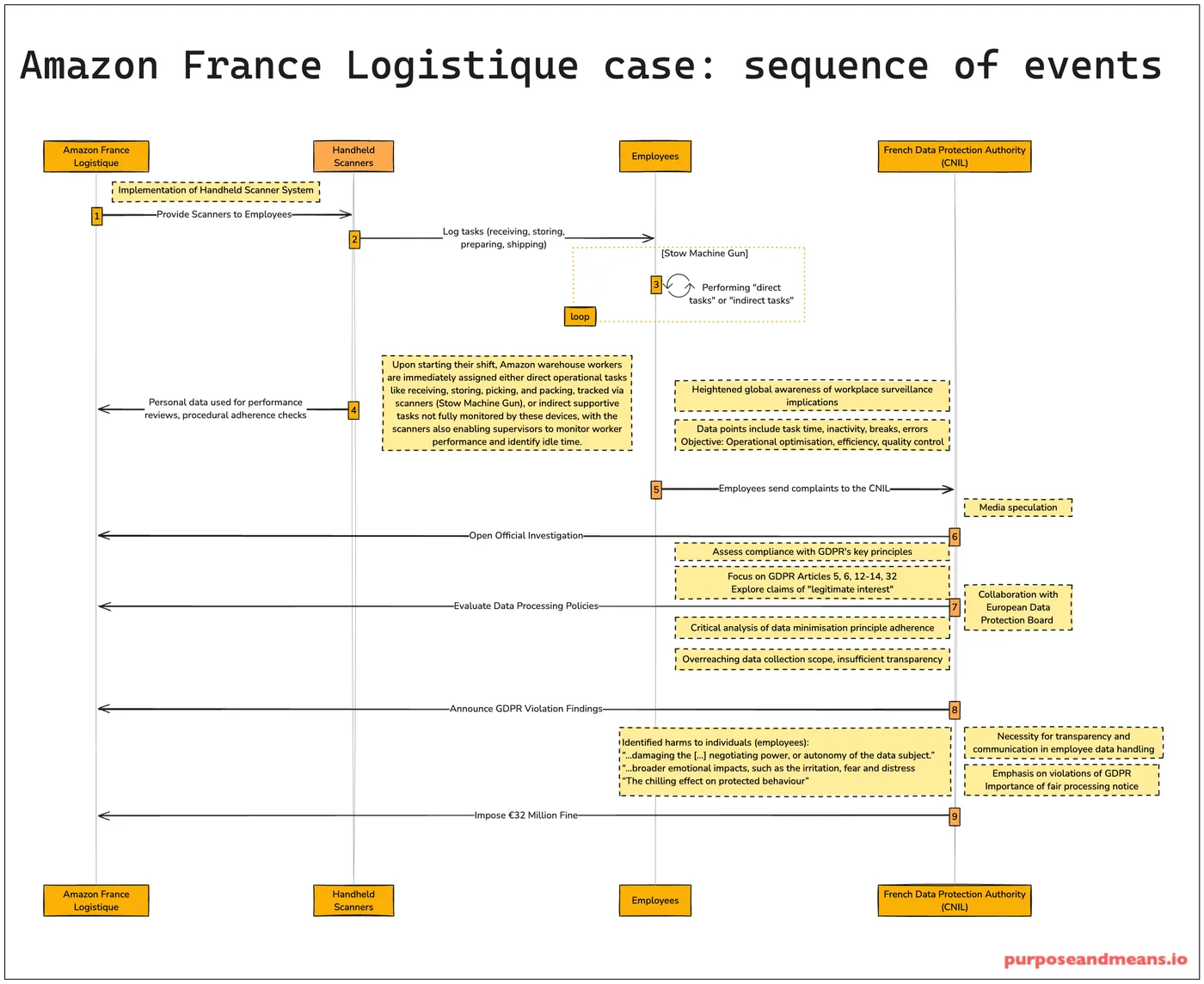
Amazon Logistique Case: Sequence of Events
Traces the steps from handheld scanner deployment through employee complaints, GDPR investigation, and the €32 million CNIL fine.
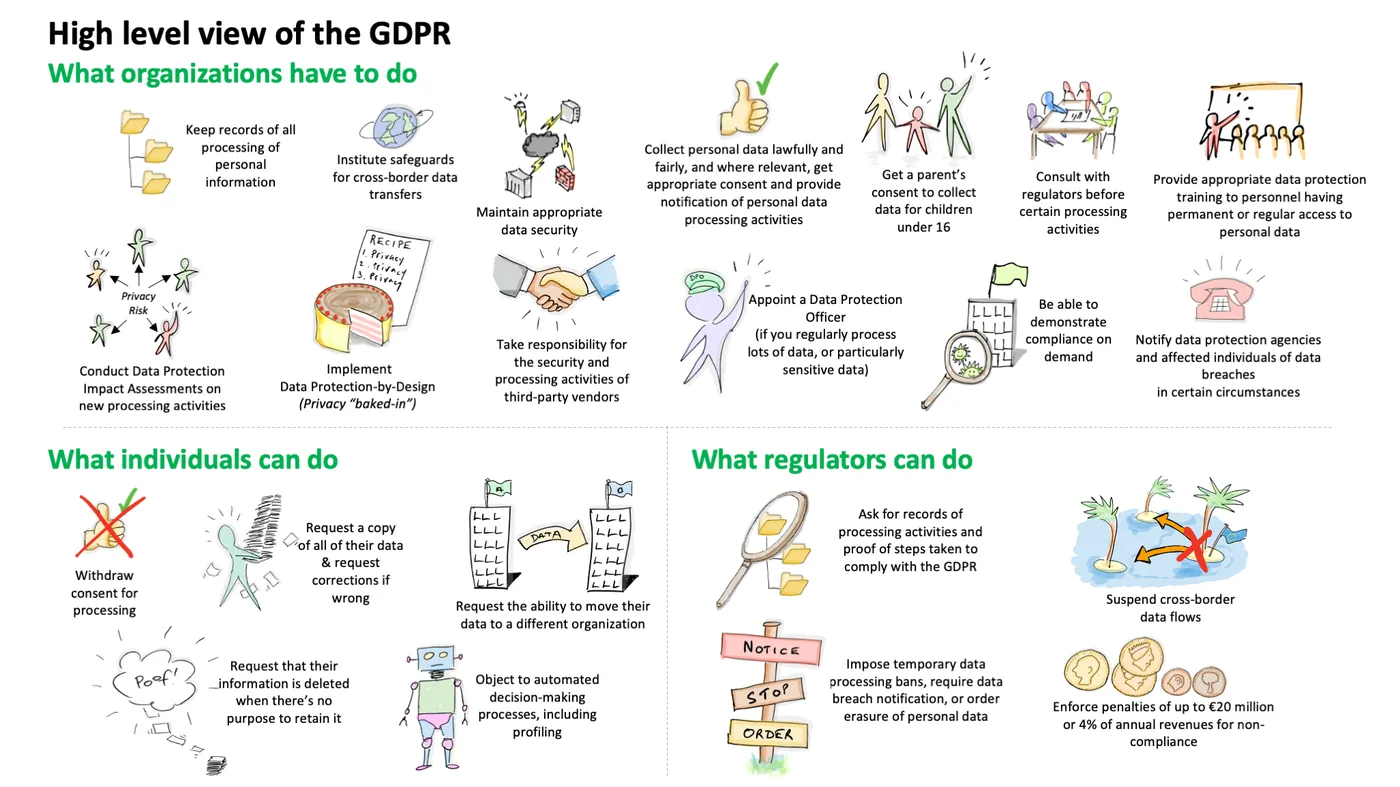
GDPR on a Page
A high-level overview of the GDPR, outlining compliance obligations, security, lawful basis, data subject rights, enforcement, and penalties.
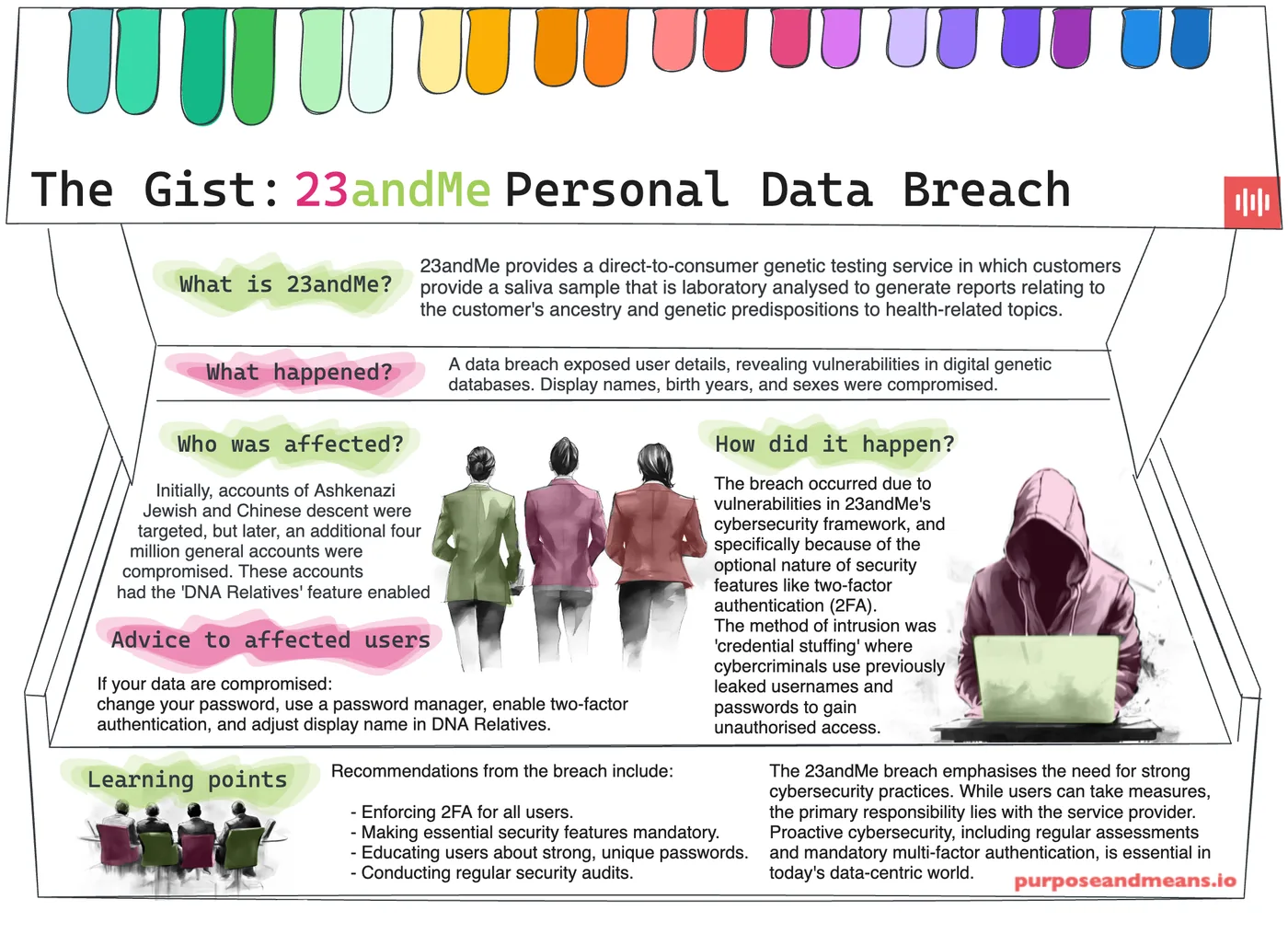
23andMe Personal Data Breach
A summary of the 23andMe data breach, describing how vulnerabilities led to compromised genetic data and targeted attacks against specific groups.
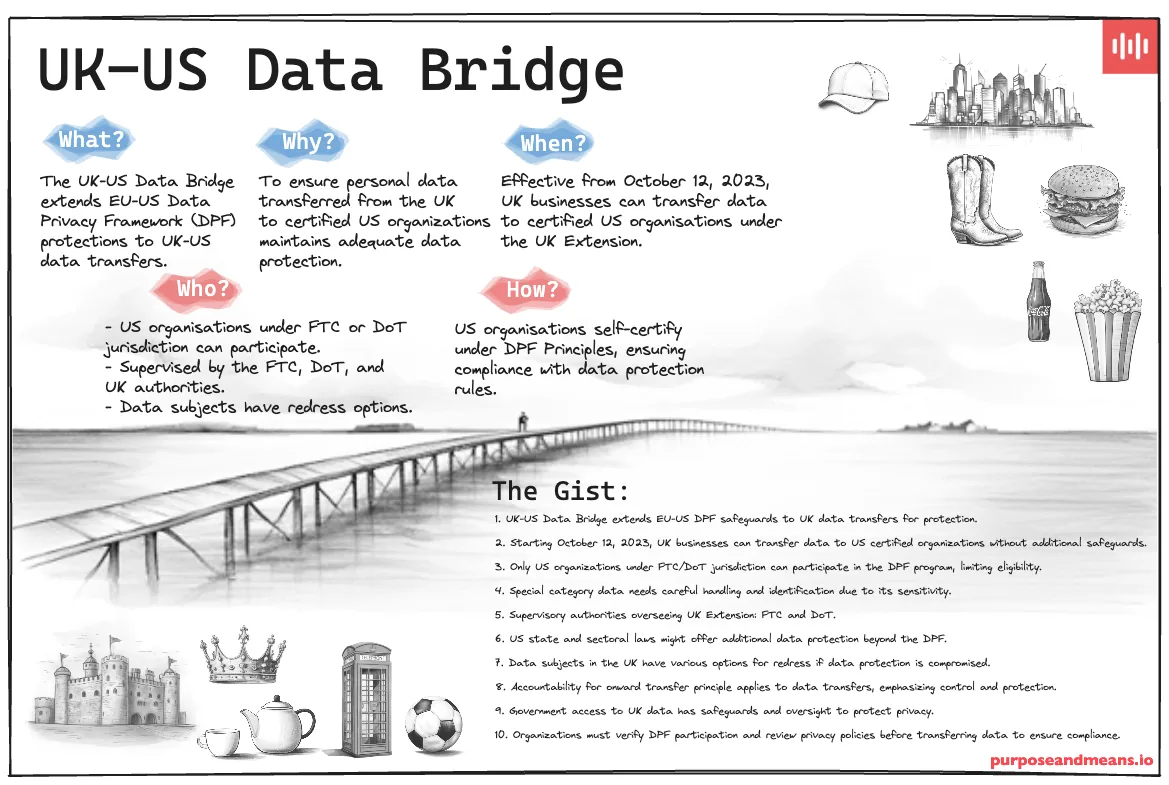
UK-US Data Bridge
Explains the UK-US Data Bridge, which extends EU-US DPF protections to UK-US data transfers under strict compliance and supervisory oversight.
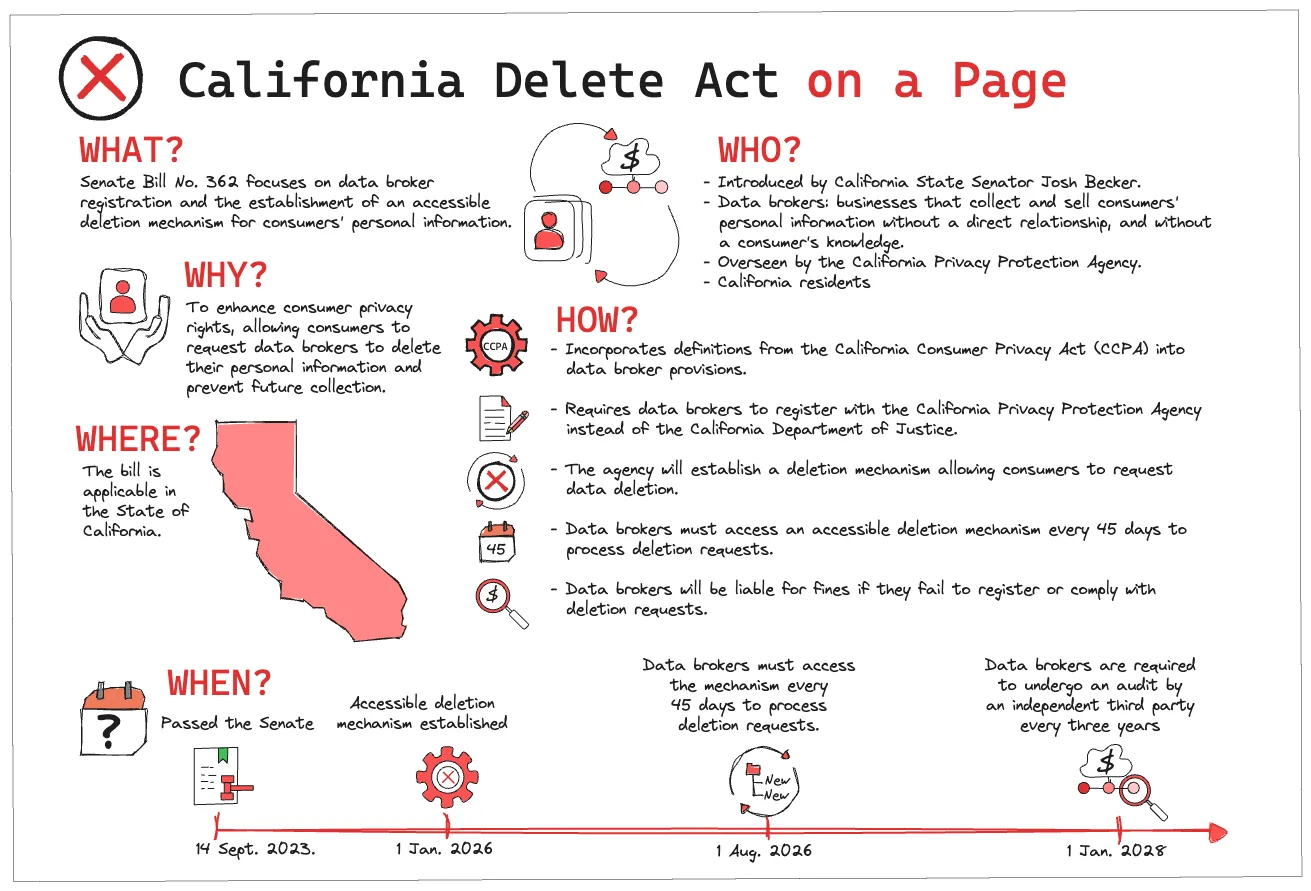
California Delete Act
Outlines new requirements for data brokers to register, provide deletion mechanisms, and enhance privacy rights for California residents.
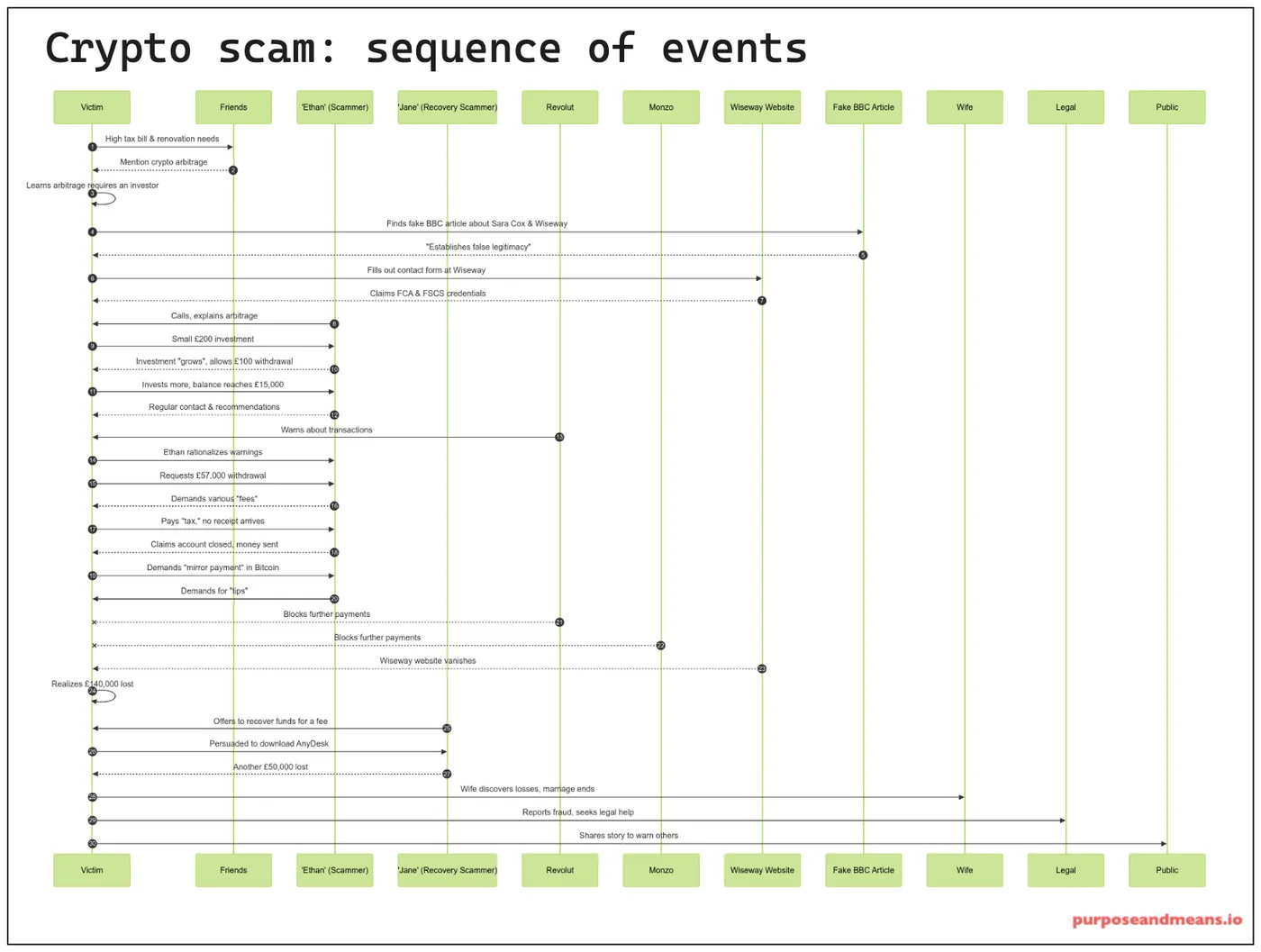
Crypto Scam: Sequence of Events
Depicts the sequence of events in a crypto scam, illustrating how victims are manipulated through false investment opportunities and staged recoveries.
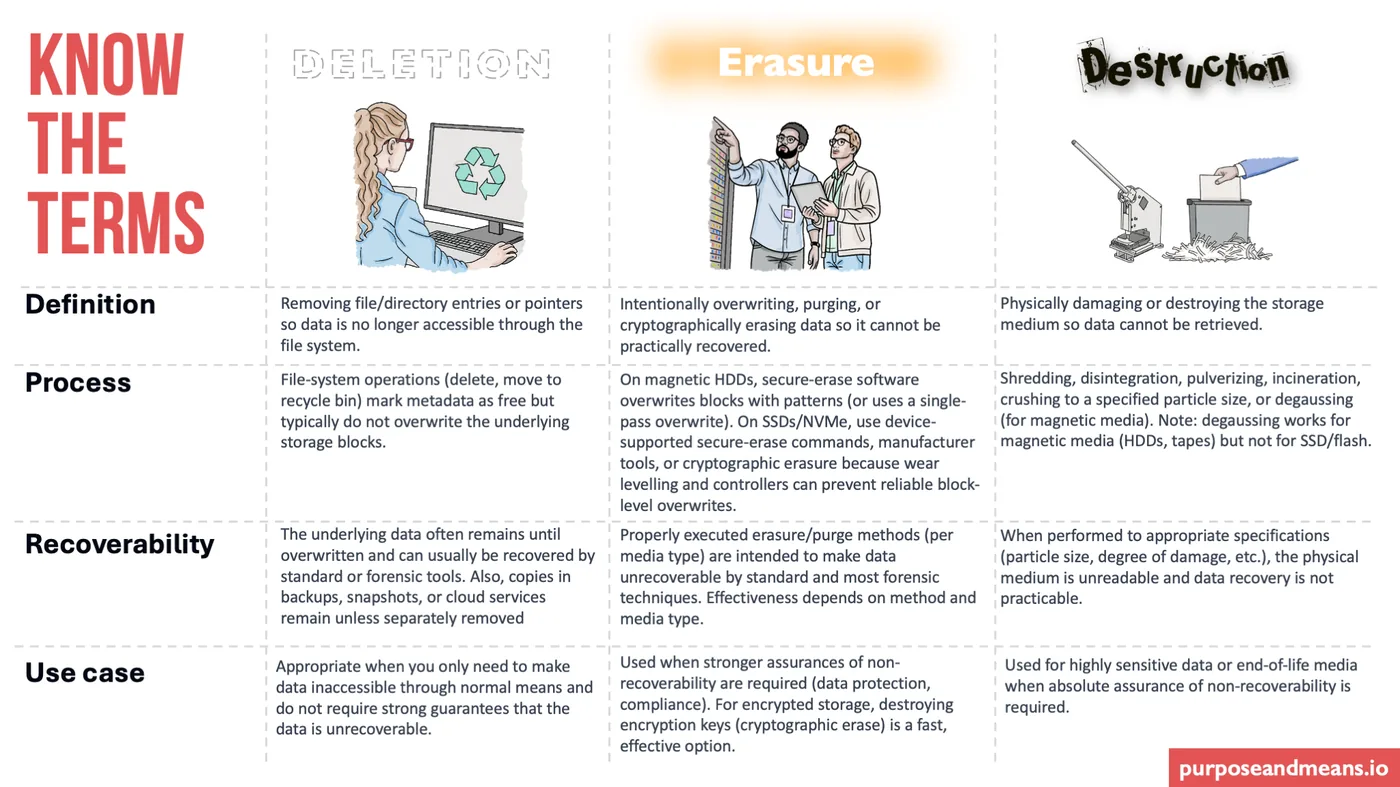
Know the Terms: Deletion, Erasure and Destruction
Data deletion, data erasure, and data destruction are often misused and misunderstood. A quick overview of what you need to know.
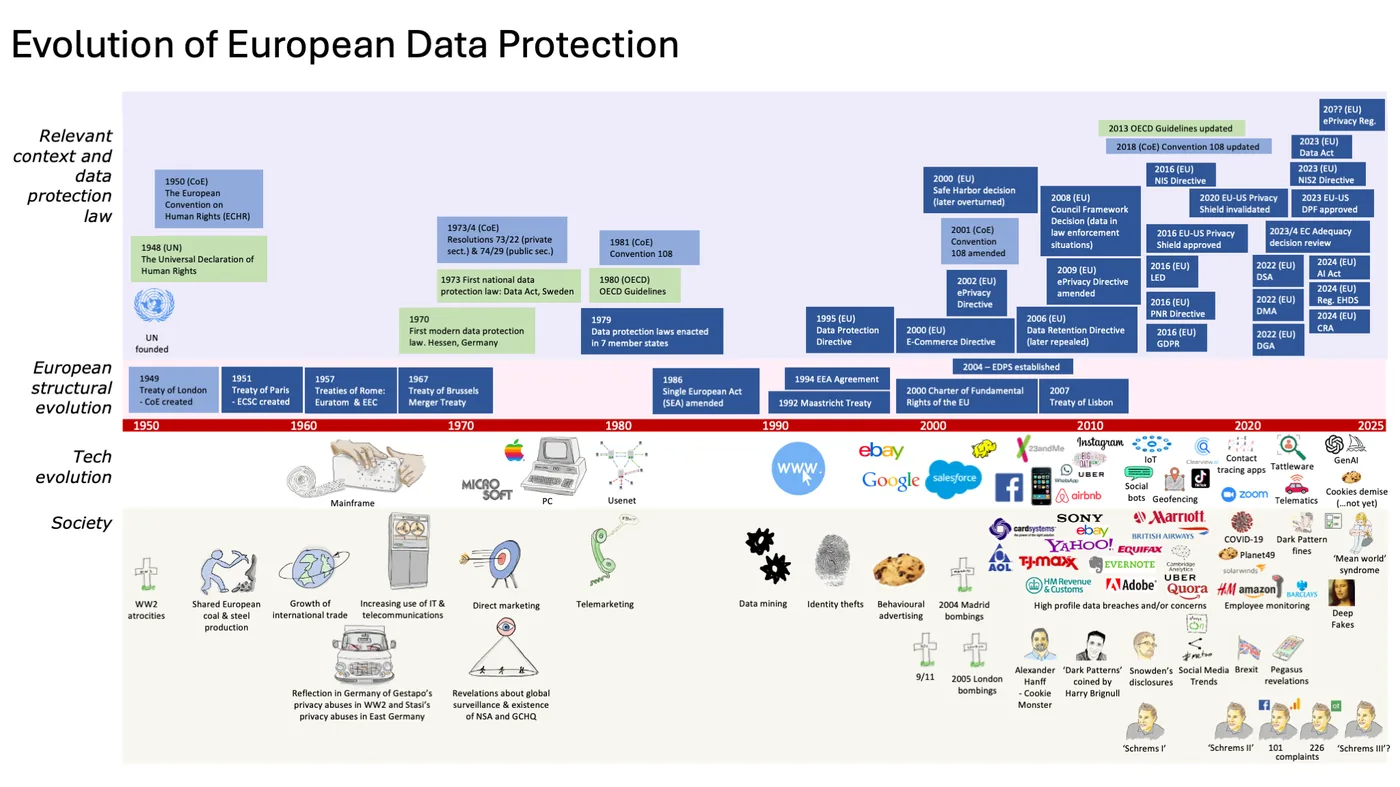
Evolution of European Data Protection (Landscape)
Chronologically illustrates the evolution of European data protection, mapping landmark laws and major societal events from 1950 to 2025.
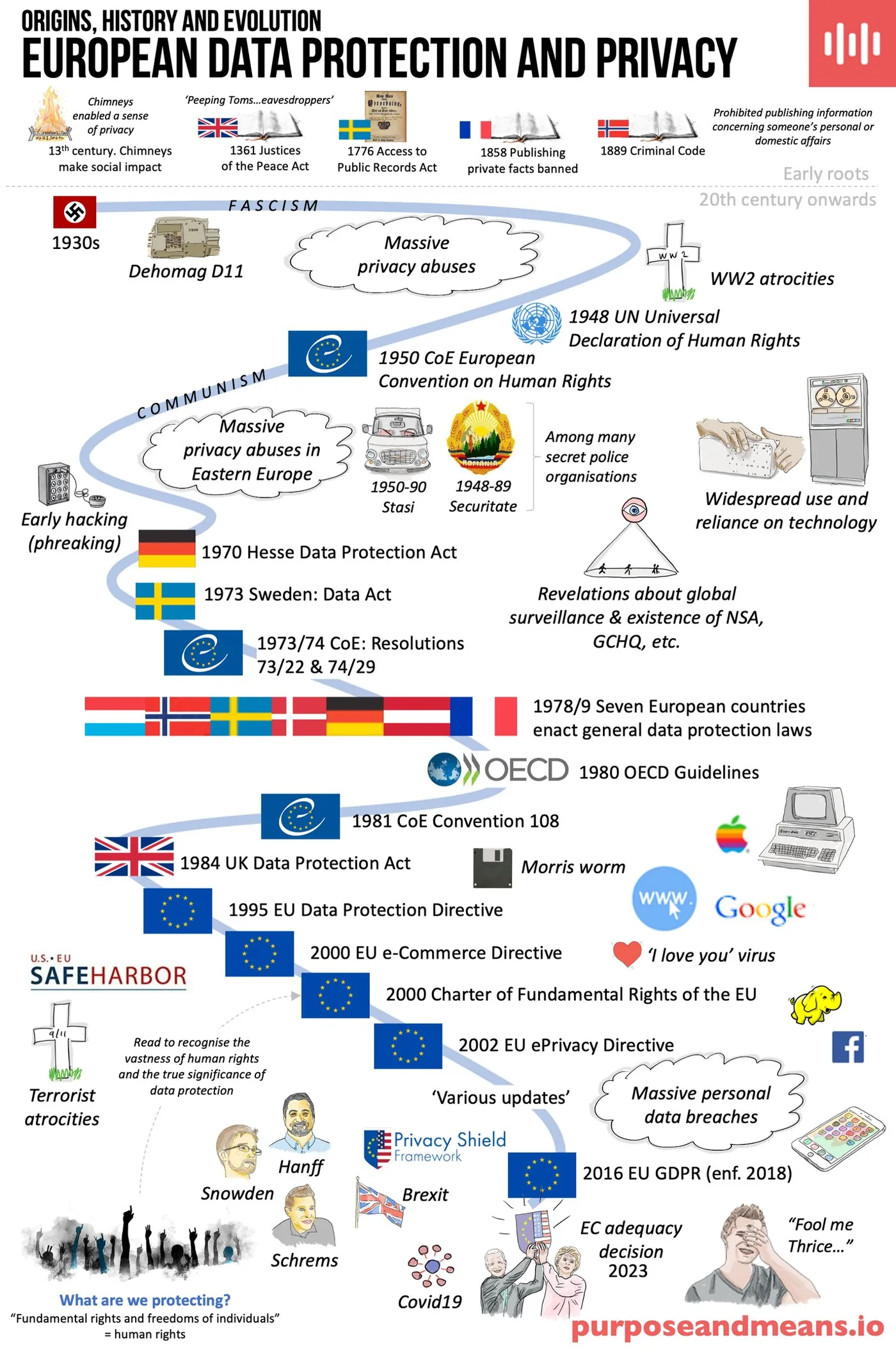
Evolution of European Data Protection (Portrait)
Portrait version of the European data protection evolution infographic, mapping landmark laws and major societal events from 1950 to 2025.
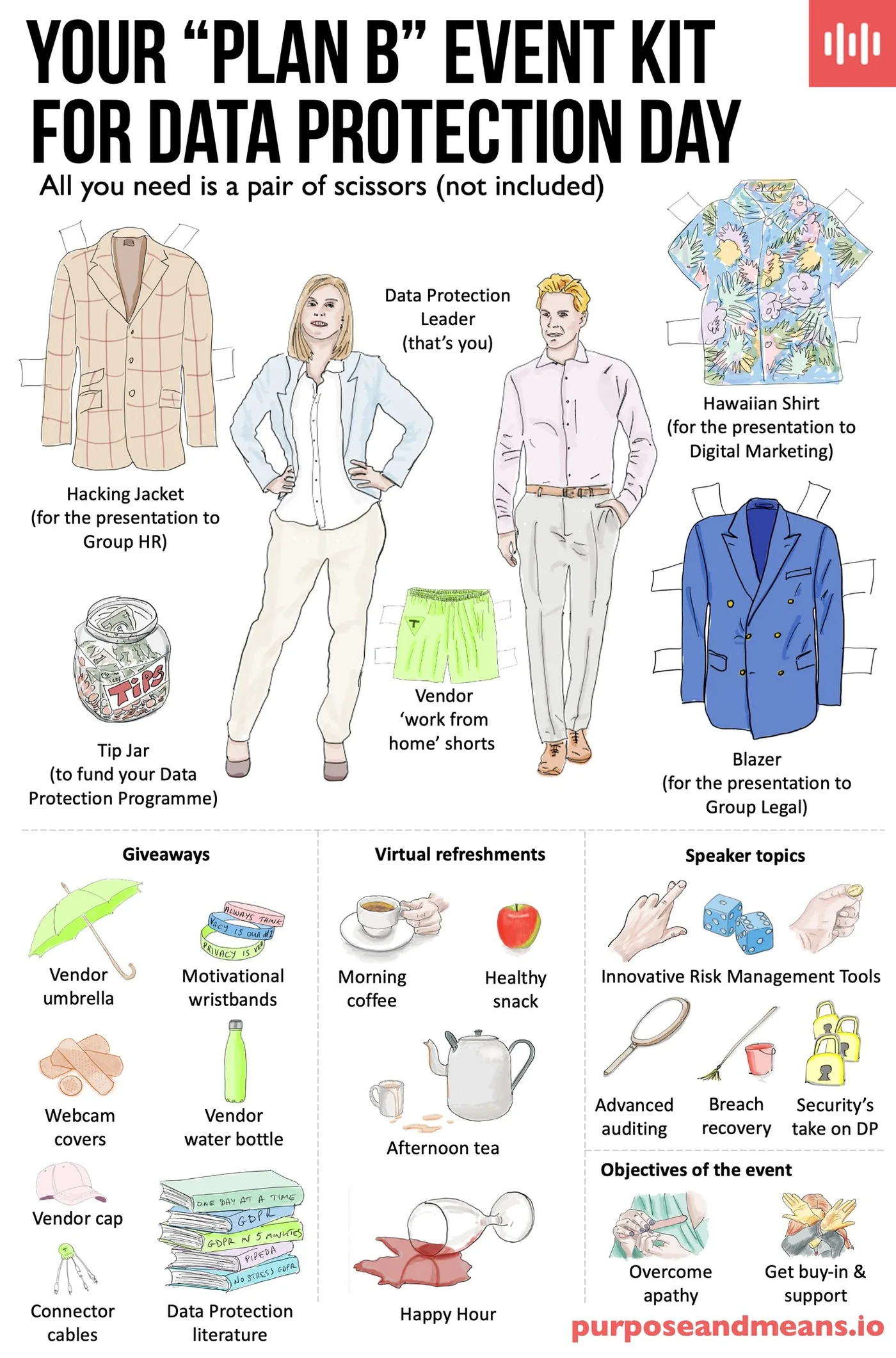
Data Protection Day Event Kit
A tongue-in-cheek "Plan B" kit for Data Protection Day events, featuring themed attire, suggested giveaways, speaker topics, and engagement objectives.
